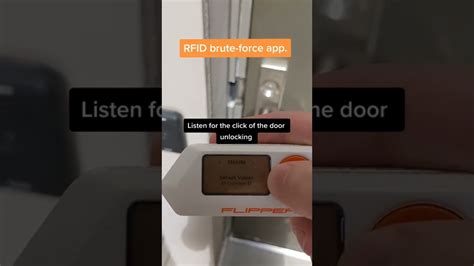
brute force rfid reader By collecting data from the reader of a door, it can figure out what passwords would unlock a key that works on that door. You still need physical access to a NFC tag that does work on that door so you can use your newly . LINQS Hub is a cloud based, enterprise grade platform to create, . Imagine the .
0 · flipperzero bruteforce
1 · brutes force nfc reader
2 · brutes force nfc
3 · bruteforce codes
on-screen tutorial to learn about each feature and how to use it. Tap the. .
Just a simple RFID authentication key brute-force program written in python, as all the ones I found were written in C. This is much more user friendly See moreUsing flipperzero-bruteforce.py you can generate bruteforce .sub files for subghz protocols that use fixed OOK codes. Inside the script it is also possible to specify your own protocol in case it's not present. To generate all the files simply run: . By collecting data from the reader of a door, it can figure out what passwords would unlock a key that works on that door. You still need physical access to a NFC tag that does work on that door so you can use your newly .
self-reconfigurable rfid reader antenna
Just a simple RFID authentication key brute-force program written in python, as all the ones I found were written in C. This is much more user friendly. Required Hardware: Mifare RC522 RFID Reader. Raspberry Pi, or a controller with GPIO pins ideally running some form of debian linux. Usage: Add any keys you wish to test to the keys.txt file.Using flipperzero-bruteforce.py you can generate bruteforce .sub files for subghz protocols that use fixed OOK codes. Inside the script it is also possible to specify your own protocol in case it's not present. To generate all the files simply run: python3 flipperzero-bruteforce.py.
By collecting data from the reader of a door, it can figure out what passwords would unlock a key that works on that door. You still need physical access to a NFC tag that does work on that door so you can use your newly calculated password to read the data from a working NFC tag to emulate. No, all readers have a 1-5 second timeout between reads so bruteforce attacks will take ages. Among other things this depends on the reader and the communication that is happening. If the reader is only reading the RFID tokens UID then it could be as few as 4 bytes, so only about 4 billion possibilities. If there is no way to read them from the card, the other 2 bytes can be brute-forced. [Video] Emulating 125 kHz RFID to open an electric door lock. To emulate an RFID tag we need to go into the menu 125 kHz RFID —> Saved, .
If an attacker captures that data from a known-valid card, the final identifier of another employee’s RFID credentials can be brute forced with significantly fewer guesses. This could allow an attacker to leverage information obtained from one employee’s card to brute force a higher level of access. All the apps that are available for flipper and named as fuzzers like the RFID/Ibutton fuzzer are in fact either brute force apps and/or apps that test generic/standard master keys.
It depends on the card technology in use. If it uses "dumb" cards/tags that merely broadcast a block of data when powered on then all it takes to defeat it is to read that data block from a legitimate card and then simulate a card transmitting that data block.Use Case: Brute-force an HID Reader A brute-force attack can be done by trying to guess multiple tag UID’s similar to a known working tag UID to gain access. You can also adjust the brute-force parameters like tag UID, facility code, format length, and replay rate. Small Arduino Program to crack by brute force a sector key of a MIRAFE/RFID tag. There are 3 version of the program. Cracker Data Logger & Serial. This version outputs the data on the serial and saves it on an SD card (Following the Wire.png Scheme). Cracker only SD.Just a simple RFID authentication key brute-force program written in python, as all the ones I found were written in C. This is much more user friendly. Required Hardware: Mifare RC522 RFID Reader. Raspberry Pi, or a controller with GPIO pins ideally running some form of debian linux. Usage: Add any keys you wish to test to the keys.txt file.
Using flipperzero-bruteforce.py you can generate bruteforce .sub files for subghz protocols that use fixed OOK codes. Inside the script it is also possible to specify your own protocol in case it's not present. To generate all the files simply run: python3 flipperzero-bruteforce.py. By collecting data from the reader of a door, it can figure out what passwords would unlock a key that works on that door. You still need physical access to a NFC tag that does work on that door so you can use your newly calculated password to read the data from a working NFC tag to emulate.
No, all readers have a 1-5 second timeout between reads so bruteforce attacks will take ages. Among other things this depends on the reader and the communication that is happening. If the reader is only reading the RFID tokens UID then it could be as few as 4 bytes, so only about 4 billion possibilities.
If there is no way to read them from the card, the other 2 bytes can be brute-forced. [Video] Emulating 125 kHz RFID to open an electric door lock. To emulate an RFID tag we need to go into the menu 125 kHz RFID —> Saved, . If an attacker captures that data from a known-valid card, the final identifier of another employee’s RFID credentials can be brute forced with significantly fewer guesses. This could allow an attacker to leverage information obtained from one employee’s card to brute force a higher level of access. All the apps that are available for flipper and named as fuzzers like the RFID/Ibutton fuzzer are in fact either brute force apps and/or apps that test generic/standard master keys.
It depends on the card technology in use. If it uses "dumb" cards/tags that merely broadcast a block of data when powered on then all it takes to defeat it is to read that data block from a legitimate card and then simulate a card transmitting that data block.Use Case: Brute-force an HID Reader A brute-force attack can be done by trying to guess multiple tag UID’s similar to a known working tag UID to gain access. You can also adjust the brute-force parameters like tag UID, facility code, format length, and replay rate.
flipperzero bruteforce
Animal Crossing themed Near Field Communication (NFC) capable amiibo cards that work with compatible games on the Nintendo Switch, Wii U and Nintendo .Custom Animal Crossing Amiibo Cards. ALL Series are Available in our store. Fast Ship from .
brute force rfid reader|brutes force nfc