credit card rfid vulnerability Leveraging RFID cards with other security measures, like security cameras, access control, and effective security protocols, is the perfect way to avoid RFID hacking. For example, implementing protocols that prevent duplicate entries allows you to eliminate the threat of credential theft.
The Reserve Bank of India’s (RBI) new credit and debit card guidelines, which came into effect from 1 October, allow you to turn near-field communications (NFC) on and off on your card at will.
0 · rfid scammers
1 · rfid scam
2 · rfid laws and regulations
3 · rfid how to block
4 · problems with rfid technology
5 · how to stop rfid scanning
6 · how to prevent rfid cloning
7 · how to block rfid scanning
You can try NFC Tools or the MiFare Classic Tool to emulate cards from your phone, but in my .
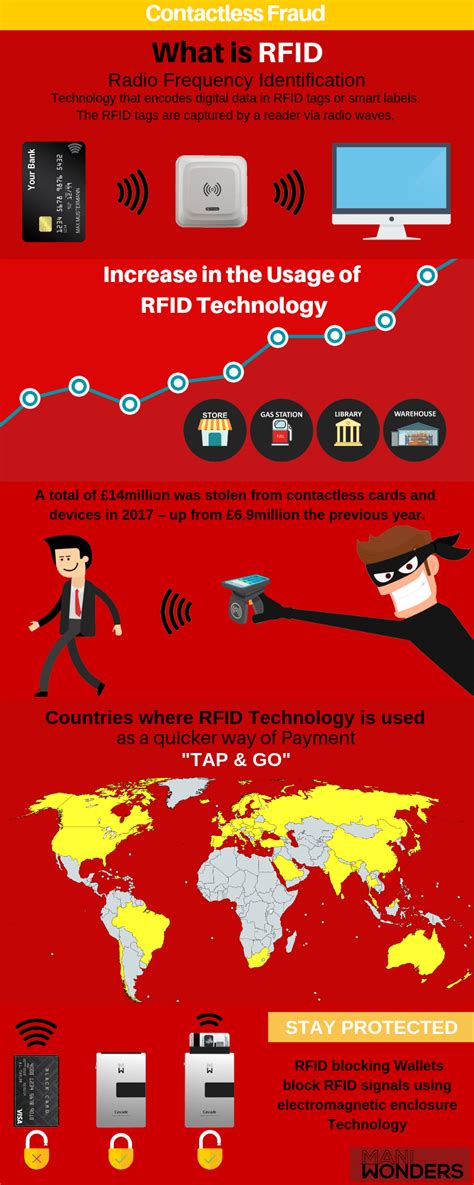
Radio-Frequency Identification (RFID) involves the use of radio waves to read and capture information stored on an electronic chip attached to an object. RFID chips, or “tags,” can . See moreWhile RFID skimming should be the least of your worries, it’s important to take steps to protect against the very real threats of credit card fraud and other forms of identity theft. Be proactive with automatic, 24/7 monitoring of your credit report and credit score, so you’ll . See moreSome security experts have voiced concerns about a phenomenon called RFID skimming, in which a thief with an RFID reader may be able to steal your credit card number or personal information simply by walking within a few feet of you. It’s a scary thought, . See more Leveraging RFID cards with other security measures, like security cameras, access control, and effective security protocols, is the perfect way to avoid RFID hacking. For example, implementing protocols that prevent .
Some security experts have voiced concerns about a phenomenon called RFID skimming, in which a thief with an RFID reader may be able to steal your credit card number or personal information simply by walking within a few feet of you.
Leveraging RFID cards with other security measures, like security cameras, access control, and effective security protocols, is the perfect way to avoid RFID hacking. For example, implementing protocols that prevent duplicate entries allows you to eliminate the threat of credential theft. [1] The most recent vulnerability is found to be in VISA contactless payment in which the attacker modifies the unauthenticated conversation between the card and terminal to bypass PIN verification. It executes relay attack using 2 NFC enabled smartphones.
Table of contents. What is an RFID card and how does it work? How secure are RFID cards? Tips for preventing credit card theft. Key takeaways. RFID credit cards are growing in.Technically all RFID cards are scannable given the right equipment. Some vendors implement protections like randomly generated keys etc, so the only surefire way to protect your cards is to wrap them in a faraday cage.
rfid scammers
The researchers claimed that the RFID chip transmitted account numbers and other sensitive information openly through the air, making them vulnerable to theft. The card companies, however, claimed the data was encrypted and that the researcher's sample -- only 20 cards -- was too small.Experimental Results: Although RFID-enabled credit cards are widely re-ported to use sophisticated cryptography [3,15,18,21,29,32], our experiments found several surprising vulnerabilities in every system we examined. We col-lected two commercial readers from two independent manufacturers and approx-imately 20 RFID-enabled credit cards issued . As the popularity of RFID-enabled credit cards as grown, however, so has concern over its vulnerability. If your credit card needs to only be near the reader for it to process, what happens if a criminal holds a reader next to your RFID-enabled credit card?
Although RFID-enabled credit cards are widely reported to use sophisticated cryptog- raphy [4,19,23,25,41,43], our experiments found several surprising vulnerabilities in every system we examined.
Security researchers at Quarkslab have discovered a backdoor in millions of RFID cards developed by Shanghai Fudan Microelectronics (FMSH). When properly exploited, this backdoor could be used.

Some security experts have voiced concerns about a phenomenon called RFID skimming, in which a thief with an RFID reader may be able to steal your credit card number or personal information simply by walking within a few feet of you. Leveraging RFID cards with other security measures, like security cameras, access control, and effective security protocols, is the perfect way to avoid RFID hacking. For example, implementing protocols that prevent duplicate entries allows you to eliminate the threat of credential theft. [1] The most recent vulnerability is found to be in VISA contactless payment in which the attacker modifies the unauthenticated conversation between the card and terminal to bypass PIN verification. It executes relay attack using 2 NFC enabled smartphones. Table of contents. What is an RFID card and how does it work? How secure are RFID cards? Tips for preventing credit card theft. Key takeaways. RFID credit cards are growing in.
Technically all RFID cards are scannable given the right equipment. Some vendors implement protections like randomly generated keys etc, so the only surefire way to protect your cards is to wrap them in a faraday cage. The researchers claimed that the RFID chip transmitted account numbers and other sensitive information openly through the air, making them vulnerable to theft. The card companies, however, claimed the data was encrypted and that the researcher's sample -- only 20 cards -- was too small.Experimental Results: Although RFID-enabled credit cards are widely re-ported to use sophisticated cryptography [3,15,18,21,29,32], our experiments found several surprising vulnerabilities in every system we examined. We col-lected two commercial readers from two independent manufacturers and approx-imately 20 RFID-enabled credit cards issued . As the popularity of RFID-enabled credit cards as grown, however, so has concern over its vulnerability. If your credit card needs to only be near the reader for it to process, what happens if a criminal holds a reader next to your RFID-enabled credit card?
Although RFID-enabled credit cards are widely reported to use sophisticated cryptog- raphy [4,19,23,25,41,43], our experiments found several surprising vulnerabilities in every system we examined.
crypto visa contactless card netherlands
coop contactless card
Amiibo data are stored on the physical Amiibo as a .bin file. .Bin file - raw data from physical Amiibo. .NFC file - the file needed to write to an NFC tag/card or send via nfc to your switch, this emulates a physical Amiibo. Note: You won't .
credit card rfid vulnerability|how to prevent rfid cloning