hacking rfid cards Hackers using RFID scanners can theoretically steal money via your phone's tap-to-pay app. Here's how to prevent RFID hacking. Aispyer, with its exceptionally interesting monitoring tools, is one of the best Android hacking apps you can install. Below is the APK link to download the hacking app. Find the APK/Download link .
0 · rfid scammers
1 · rfid scam
2 · rfid how to block
3 · rfid hacking tool
4 · is rfid safe to hack
5 · how to stop rfid scanning
6 · how to prevent rfid cloning
7 · how to block rfid scanning
Với thẻ Card Visit NFC bạn chủ động cung cấp thông tin cho người bạn muốn .
RFID cards and tags can be rendered useless by hackers who generate a stronger signal than the RFID reader. This not only disrupts inventory tracking but also causes chaos by blocking access with ID cards.
Access credentials are prone to hacking. This post explains how easy it is to copy access cards with Flipper Zero, off-the-shelf hardware, and an app. 10 min reading time. Updated on January 19, 2024. Written by Bernhard . RFID cards and tags can be rendered useless by hackers who generate a stronger signal than the RFID reader. This not only disrupts inventory tracking but also causes chaos by blocking access with ID cards.
Hackers using RFID scanners can theoretically steal money via your phone's tap-to-pay app. Here's how to prevent RFID hacking. Access credentials are prone to hacking. This post explains how easy it is to copy access cards with Flipper Zero, off-the-shelf hardware, and an app. 10 min reading time. Updated on January 19, 2024. Written by Bernhard Mehl. Share this article.
Ever wondered how easy it is to hack an RFID card? In this blog, I’ll show you the basics of RFID technology and how to clone a card using tools like Proxmark3 and MIFARE magic cards. The latest update is all about RFID and NFC, and how the Flipper Zero can interact with a variety of contactless protocols. Popular 125 kHz protocols: EM-Marin, HID Prox II, and Indala. Hackers can and have jammed RFID cards and tags from working simply by being nearby and generating a signal that is stronger than the one being put out by the RFID reader. This can make it impossible to track inventory using RFID, while also creating general havoc by preventing access using ID cards. Eavesdropping. Radio Frequency Identification (RFID), is a technology that uses electromagnetic fields to automatically identify and/or track “tags” that contain electronically stored information. Some tags are passive, therefore they are activated by the electromagnetic fields generated by nearby readers.
The ChameleonMini is a tool that allows you to emulate and clone high-frequency contactless cards and read RFID tags. It functions as an NFC emulator and RFID reader and can sniff and log.
By tampering with the RFID tags, they could manipulate the information about the contents of the materials, leading to potential accidents or security breaches. These examples illustrate the real-world impact of RFID hacking and emphasize the importance of .This project demonstrates how to exploit vulnerabilities in NFC cards using Arduino and RFID technology. It provides a basic framework for reading and writing NFC cards using the MFRC522 RFID module. RFID cards and tags can be rendered useless by hackers who generate a stronger signal than the RFID reader. This not only disrupts inventory tracking but also causes chaos by blocking access with ID cards.
Hackers using RFID scanners can theoretically steal money via your phone's tap-to-pay app. Here's how to prevent RFID hacking.
Access credentials are prone to hacking. This post explains how easy it is to copy access cards with Flipper Zero, off-the-shelf hardware, and an app. 10 min reading time. Updated on January 19, 2024. Written by Bernhard Mehl. Share this article. Ever wondered how easy it is to hack an RFID card? In this blog, I’ll show you the basics of RFID technology and how to clone a card using tools like Proxmark3 and MIFARE magic cards. The latest update is all about RFID and NFC, and how the Flipper Zero can interact with a variety of contactless protocols. Popular 125 kHz protocols: EM-Marin, HID Prox II, and Indala. Hackers can and have jammed RFID cards and tags from working simply by being nearby and generating a signal that is stronger than the one being put out by the RFID reader. This can make it impossible to track inventory using RFID, while also creating general havoc by preventing access using ID cards. Eavesdropping.
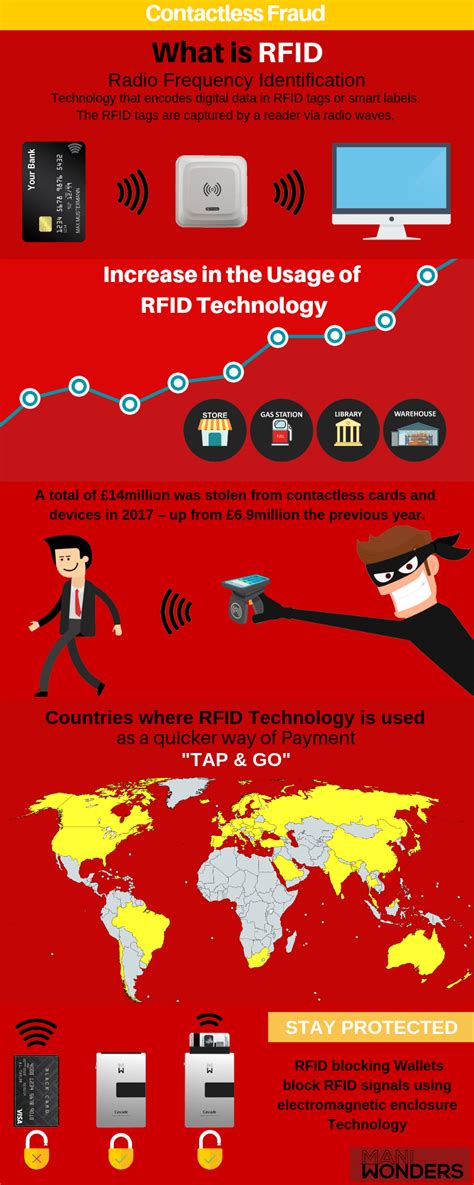
Radio Frequency Identification (RFID), is a technology that uses electromagnetic fields to automatically identify and/or track “tags” that contain electronically stored information. Some tags are passive, therefore they are activated by the electromagnetic fields generated by nearby readers. The ChameleonMini is a tool that allows you to emulate and clone high-frequency contactless cards and read RFID tags. It functions as an NFC emulator and RFID reader and can sniff and log.By tampering with the RFID tags, they could manipulate the information about the contents of the materials, leading to potential accidents or security breaches. These examples illustrate the real-world impact of RFID hacking and emphasize the importance of .
vera bradley cotton smartphone wristlet with rfid protection

rfid scammers
a) The NFC-Reader is sending data by sending a command APDU to the NFC Smart Card. b) The NFC Smart Card answers the command by sending a response APDU to the NFC .
hacking rfid cards|how to block rfid scanning