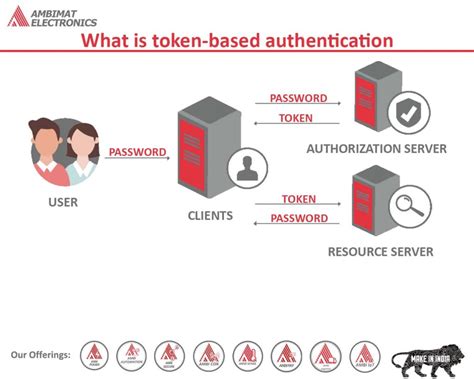
token-based card access control system Token-based authentication is different from traditional password-based or server-based authentication techniques. Tokens offer a second layer of security, and administrators have detailed control over each action and transaction. But . Bike/Car Sharing - Authentication Solutions by ELATEC
0 · what is token based authentication
1 · token based authentication entrust
2 · token based authentication control
3 · token based authentication api
4 · token based access control
5 · okta token based authentication
6 · identity provider token based authentication
7 · how to get token based authentication
If you having trouble scanning your passport with your NFC-enabled device, try these steps: 1. Remove your phone and passport from any wallets, cases, or added protective covers. 2. Lay your . See more
what is token based authentication
Token-based authentication is different from traditional password-based or server-based authentication techniques. Tokens offer a second layer of security, and administrators have detailed control over each action and transaction. But using tokens requires a bit of coding .Token-based authentication is a passwordless security mechanism that validates a user's identity through the use of tokens. A token is a unique piece of data, often a string of characters, that .Second, this paper proposes a solution by giving the general data structure of access control token, elaborating the equivalence, split, merge and verification algorithms of access control .Token-based authentication is an authentication protocol where users verify their identity in exchange for a unique access token. Users can then access the website, application, or .
Token-based authentication is different from traditional password-based or server-based authentication techniques. Tokens offer a second layer of security, and administrators have detailed control over each action and transaction. But .Token-based authentication is a passwordless security mechanism that validates a user's identity through the use of tokens. A token is a unique piece of data, often a string of characters, that acts as a stand-in for the user's credentials.
new design rf eas security tag
Second, this paper proposes a solution by giving the general data structure of access control token, elaborating the equivalence, split, merge and verification algorithms of access control token, and explaining the system architecture of token-based access control.Token-based authentication is an authentication protocol where users verify their identity in exchange for a unique access token. Users can then access the website, application, or resource for the life of the token without having to re-enter their credentials. The microservice access control method is based on a token strategy that increases security in access control by distinguishing between authentication and authorization services, the issued tokens of which are trusted by the resource microservices.Token-based authentication is the process of verifying identity by checking a token. In access management, servers use token authentication to check the identity of a user, an API, a computer, or another server.

Access control is one of the most basic and essential security measures used in data centers. It is underpinned by effective user authentication measures. Choosing the right combination of access control and authentication measures is key to effective data center security. Here is a quick guide to what you need to know. Second, this paper proposes a solution by giving the general data structure of access control token, elaborating the equivalence, split, merge and verification algorithms of access control.
Token-Based Access Control is a security technique where a validated user is given a digital token, enabling them to access a system or network. Social media platforms, online banking, and cloud services like Google Drive and Dropbox frequently use this . Token-based access control (TBAC) enhances the manageability of authorization through the token. However, traditional access control policies lack the ability to dynamically adjust based on user access behavior. Incorporating user reputation evaluation into access control can provide valuable feedback to enhance system security and flexibility. Token-based authentication is different from traditional password-based or server-based authentication techniques. Tokens offer a second layer of security, and administrators have detailed control over each action and transaction. But .Token-based authentication is a passwordless security mechanism that validates a user's identity through the use of tokens. A token is a unique piece of data, often a string of characters, that acts as a stand-in for the user's credentials.
Second, this paper proposes a solution by giving the general data structure of access control token, elaborating the equivalence, split, merge and verification algorithms of access control token, and explaining the system architecture of token-based access control.
Token-based authentication is an authentication protocol where users verify their identity in exchange for a unique access token. Users can then access the website, application, or resource for the life of the token without having to re-enter their credentials.
The microservice access control method is based on a token strategy that increases security in access control by distinguishing between authentication and authorization services, the issued tokens of which are trusted by the resource microservices.Token-based authentication is the process of verifying identity by checking a token. In access management, servers use token authentication to check the identity of a user, an API, a computer, or another server. Access control is one of the most basic and essential security measures used in data centers. It is underpinned by effective user authentication measures. Choosing the right combination of access control and authentication measures is key to effective data center security. Here is a quick guide to what you need to know.
token based authentication entrust
Second, this paper proposes a solution by giving the general data structure of access control token, elaborating the equivalence, split, merge and verification algorithms of access control. Token-Based Access Control is a security technique where a validated user is given a digital token, enabling them to access a system or network. Social media platforms, online banking, and cloud services like Google Drive and Dropbox frequently use this .
token based authentication control
token based authentication api
Just unlock your phone and tap the Tag. It will read just fine and show the notification without the need of opening tag reader. iPhones XS and up try to read NFC tags in the background all the time. Therefore manual reading was never .Posted on Nov 1, 2021 12:10 PM. On your iPhone, open the Shortcuts app. Tap on the Automation tab at the bottom of your screen. Tap on Create Personal Automation. Scroll down and select NFC. Tap on Scan. Put your iPhone near the NFC tag. Enter a name for your tag. .
token-based card access control system|what is token based authentication